A person’s usability within FlowWorks is determined by two things:
- The role(s) they have been assigned.
- The Security Group(s) to which they belong.
You can assign one or more user roles and security groups to each user in your client base. The proper mix of capabilities and access can permit a user to perform his/her assigned functions.
Please read this article carefully before creating new users, to ensure the security of your entire user network is well maintained!
Definitions
Client: An organization subscribed to FlowWorks' software services.
User: An individual working under a client, who logs-in to FlowWorks using their own login credentials.
Role: A user’s assigned function(s) and responsibilities in FlowWorks. Roles are useful for limiting or extending a user’s accessibility to tools (such as F.A.C.E and Alarming) and administrative functions (such as creating and managing user accounts).
Security Group: A set of permissions that dictate the visibility & accessibility of sites & channels, and custom-made resources (including GIS layers, custom apps and custom screens).
Overall structure
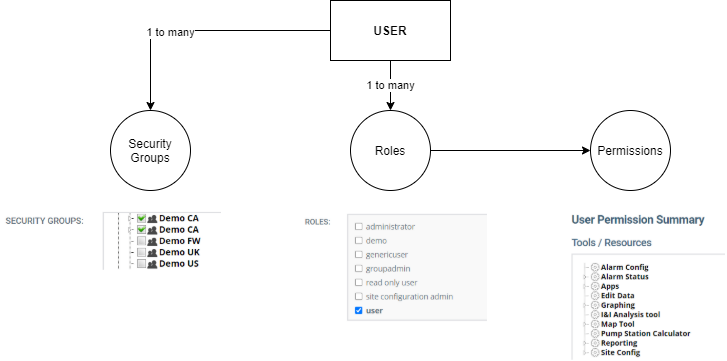
A client of FlowWorks can have from one to many individual users. The flowchart shown above demonstrates that a single user must be assigned a role and be part of a security group, although each user can be assigned more than one of each. Every role-type dictates the tools and administrative privilege a user has access to; a security group determines the scope of a user’s visibility of (and accessibility to) sites, channels, and custom resources.
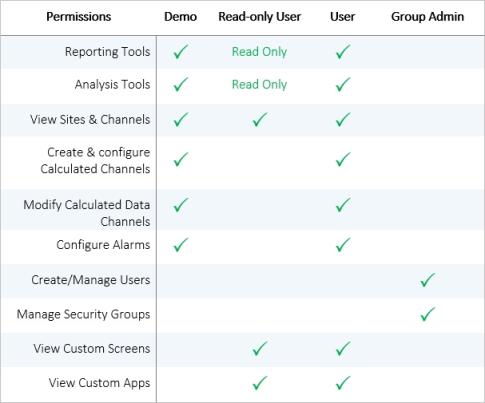
User roles
User roles determine the permissions that are appended to a user account. A single user can have more than one role.
Important notes about user roles
- A role does not ‘inherit’ the privileges of the roles below it. For example, the attributes of the ‘User’ role do not carry over to that of ‘Group Administrator’. For a Group Administrator to be fully capable of using any of the tools in FlowWorks, he/she must also be given the additional role of User. This characteristic allows greater flexibility for security and access.
- With that said, it is possible to create a user with a ‘Group Administrator’ role-type only. Without having the ‘User’ role-type as well, he/she can only create and manage other accounts and cannot fully use the features and functions offered in FlowWorks.
To find out how to check and modify the roles assigned to a user, see, Modify / Check User Roles.
User role types
The chart below describes the different types of roles that can be assigned to FlowWorks users. Remember, a user can be assigned more than one of these roles for greater access to features and control.
Security Groups
Security Groups give Group Administrator(s) the power to maintain granular control over their network of sites, channels, and custom resources.
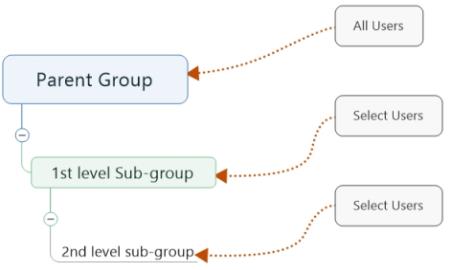
By default, each Client has a parent security group and each new user is automatically placed in this group. The parent security group entails the widest network of sites, channels, tools to which a user is permitted access. Note that all user role settings remain active in security groups.
Group Administrators can modify the settings of each security group and organize users accordingly – this is useful for sub-dividing accessibility to certain tools and visibility of sites, channels and custom resources. Parent security groups can have numerous 1st level sub-groups; and sub-groups can have numerous 2nd level sub-groups, which can have 3rd level sub-groups, and so on.
Important notes about security groups
- If a user is assigned to a sub-group, the settings of that group will take precedence over the settings of the parent group.
- It is possible to build a security structure that becomes cumbersome to manage and maintain. It is recommended that the Group Administrator(s) invest some time in planning the necessity of permitting/restricting access to sites, channels, and tools prior to creating security groups and assigning users thereto.
To find out how to create and edit Security Groups, please see article Manage Security Groups.

0 Comments